- Date
What Is a DPA? A Privacy Guide for Analytics
 Andrii Romasiun
Andrii Romasiun
A visitor creates an account on your software platform. Your database stores their email address, while an analytics provider records the geographic location of the visit. A marketing tool then triggers an onboarding sequence based on that action. Customer data moves across three different companies within seconds.
This data sharing creates legal liability. You control the customer relationship. External vendors process the information to deliver your product. A Data Processing Agreement dictates the rules for this exact exchange.
A Data Processing Agreement forms a binding contract between a business and a third-party vendor. It defines the scope, security, and purpose of personal data processing. Without this document, sharing customer data violates multiple international privacy laws.
Review your vendor list. Identify every external service touching your user data. Secure a signed contract governing data usage with each provider.
Understanding the Basics: What is a DPA?
Defining Data Controllers vs. Data Processors
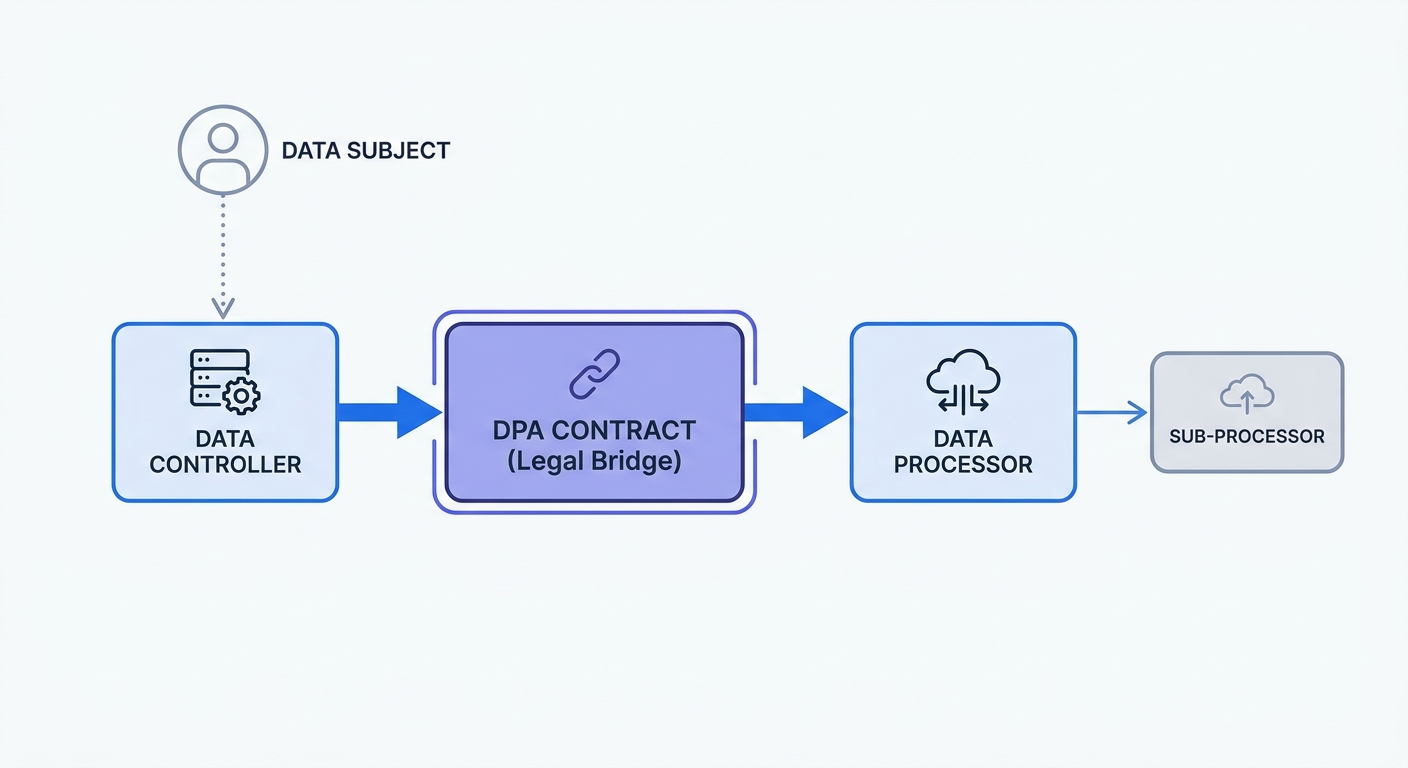
Data privacy laws assign distinct roles to companies handling user information. The Data Controller determines the purpose and method of processing personal data. Your decision regarding what information to collect and how to use it makes you the Data Controller.
The Data Processor acts on behalf of the Controller. Email marketing platforms, cloud storage providers, and web analytics tools fall into this category. They receive instructions from you, executing tasks using your data.
These roles dictate legal obligations. Controllers carry primary responsibility for obtaining user consent. Processors maintain infrastructure security and follow the Controller's commands.
Certain vendors act as both. A payment gateway processes transactions for you while acting as a controller for fraud prevention data. Define these boundaries in writing.
Map your vendor ecosystem using a classification table:
| Vendor Type | Role | Example Service | Data Handled |
|---|---|---|---|
| Analytics | Processor | Swetrix | Browser metrics, performance data |
| Cloud Hosting | Processor | AWS | Application databases |
| Payment | Joint | Stripe | Credit card details, billing addresses |
| CRM | Processor | Salesforce | Customer contact records |
Open your tech stack documentation. Assign a controller or processor label to every third-party service. Request a signed agreement from every processor on the list to avoid regulatory fines.
Is a DPA Legally Mandatory?
A handshake agreement provides zero legal protection. Regulators demand formal contracts. Article 28 of the General Data Protection Regulation mandates a written contract between controllers and processors, and the UK GDPR contains identical requirements.
US regulations impose similar mandates. The California Consumer Privacy Act demands service provider agreements to restrict data usage. Without these contracts, regulators classify third-party data sharing as a "sale" of personal information.
Ignoring this requirement guarantees compliance failures. Regulators audit paperwork before examining technical security. A missing contract triggers immediate penalties regardless of whether a data breach occurred.
Audit your compliance stack. Download the standard agreement templates from your vendor dashboards. Counter-sign these documents and store them in a centralized compliance folder.
The Hidden Risks and Fines of DPA Violations
Rising Fines for Missing DPAs
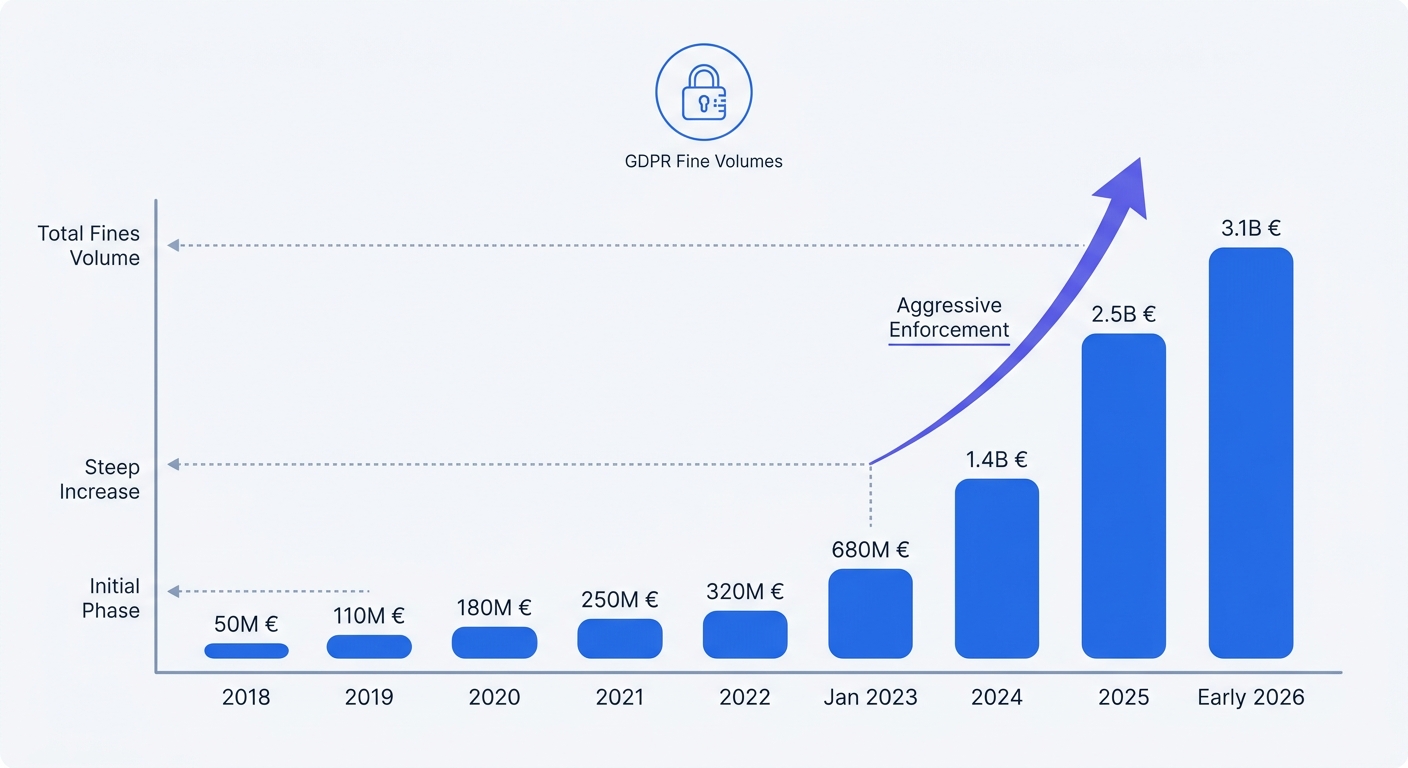
Regulatory agencies enforce paperwork rules with aggressive financial penalties. The leniency period for early GDPR adoption ended years ago. Enforcement agencies target small and medium enterprises alongside major tech corporations.
Article 83 of the GDPR dictates the penalty structure for contract violations. Supervisory authorities calculate fines based on the severity of the infringement. Neglecting to sign vendor contracts triggers Tier 1 administrative fines. These penalties reach €10 million or 2% of global annual turnover.
Between 2018 and 2025, the global average GDPR fine reached approximately €2.14 million, though penalties vary widely based on company size and violation severity. These penalties punish negligent administrative practices.
Missing Article 28 clauses cost companies millions. The French data protection authority fined software publisher Dedalus Biologie €1.5 million following a data leak. The penalty punished the company's failure to include mandatory contractual obligations in their maintenance agreements. Authorities viewed the missing contract as a distinct violation separate from the leak itself.
Check your vendor agreements for Article 28 language. Search for clauses detailing data deletion, security audits, and breach notification timelines. Replace any generic non-disclosure agreements with a proper Data Processing Agreement.
Third-Party Data Breach Liabilities
Outsourcing data processing does not outsource your legal liability. If a vendor experiences a breach, regulators hold you accountable for vendor selection. They require proof of your vendor vetting process.
Vendors introduce immense risk into your network. External actors and third-party software providers contribute to a significant portion of enterprise data breaches, with exact rates varying heavily by industry. A weak contract leaves you responsible for a partner's poor security practices.
Your contract must dictate security protocols. Specify encryption standards for data at rest and in transit. Mandate access controls for vendor employees handling your information. Require vendors to notify you of a security incident within 24 hours.
Draft an incident response plan. Include the communication steps your team will take when a vendor reports a breach. Document the timeline for notifying your supervisory authority to maintain continuous compliance.
Anatomy of a Compliant DPA
Mapping Data with a RoPA
You cannot govern unmapped data. Drafting an effective contract requires complete visibility into your information flows. Article 30 of the GDPR requires organizations to maintain a Record of Processing Activities.
A RoPA catalogs every piece of personal data your business touches. The document details collection methods, storage locations, and retention periods. It lists the exact vendors receiving specific data points.
Build your record in a spreadsheet before drafting vendor contracts. Include these columns in your data map:
- Data subject category (customers, employees, website visitors)
- Personal data categories (names, IP addresses, payment details)
- Processing purpose (marketing, order fulfillment, site analytics)
- Retention schedule (30 days, 1 year, indefinite)
- Vendor storage location (Frankfurt server, US East server)
Use this map to customize your contracts. A vendor processing email addresses requires different security stipulations than a vendor handling credit card numbers. Tailor the liability caps and security requirements based on the data sensitivity outlined in your record.
Implement an annual data map review. Schedule a meeting with your engineering and marketing teams every January. Update the document to reflect new software integrations and discontinued services.
Managing Sub-Processors and SCCs
Data processors rely on interconnected systems. They use cloud infrastructure, content delivery networks, and specialized APIs to deliver their services. These downstream vendors function as sub-processors.
Your contract must govern sub-processor usage. Processors cannot hire new vendors without your authorization. Regulators require controllers to maintain oversight of the entire data supply chain.
Include a sub-processor approval clause. Demand a minimum 30-day notice before your vendor introduces a new sub-processor. Retain the right to object to the new vendor or terminate the contract without penalty.
Geographic boundaries introduce complexity. Sharing user information across international borders requires additional legal frameworks. If your vendor transfers European data to a jurisdiction lacking an adequacy decision, implement Standard Contractual Clauses.
SCCs provide pre-approved legal language guaranteeing European privacy standards in foreign jurisdictions. Append these clauses to your main contract when using foreign vendors. Complete a Transfer Impact Assessment to verify the destination country's surveillance laws do not compromise user rights.
Bypass international transfer paperwork by selecting vendors hosting data within the European Union. Confirm their server locations in writing. Request infrastructure diagrams to ensure backups do not cross borders.
Modern DPA Challenges: AI and International Transfers
Regulating AI Sub-Processors
Artificial intelligence features change the scope of data processing. Vendors launching AI tools rewrite their terms of service to claim training rights on customer data. This unapproved usage violates user consent principles.
Data Protection Authorities scrutinize AI models. The European Data Protection Board issued guidance in 2024 regarding personal data processing in AI systems. Regulators demand clear contractual definitions regarding model training.
A standard agreement template fails to address generative AI risks. Your contracts must state whether vendors can feed your customer data into machine learning algorithms. Silence on this issue exposes your company to regulatory action.
Update your master templates. Insert a prohibition clause preventing vendors from using controller data to train, fine-tune, or improve generalized AI models. Restrict processing to the delivery of the requested service.
Review the terms of service for your existing SaaS tools. Opt out of data sharing programs in vendor dashboards. Send formal addendums to any vendor utilizing generative AI features in their core product.
Managing Cross-Border Data Rules
Regulators audit international data flows. Adequacy decisions dictate which countries offer sufficient privacy protections. These decisions face constant legal challenges and expiration dates.
The continuous shifting of data corridors creates a compliance burden. A contract signed in 2024 might become invalid in 2026 if a regional adequacy status changes. Businesses relying on foreign processors face ongoing legal friction.
Mitigate this risk through strict data localization. Choose regional software providers. Document the geographic location of every server touching your user data.
Audit your analytics and marketing stack for foreign data transfers. Read the web privacy regulations governing your primary user base. Move processing tasks to domestic vendors to eliminate transfer impact assessments.
Web Analytics, Privacy, and Simplified DPAs
The Burden of Traditional Trackers
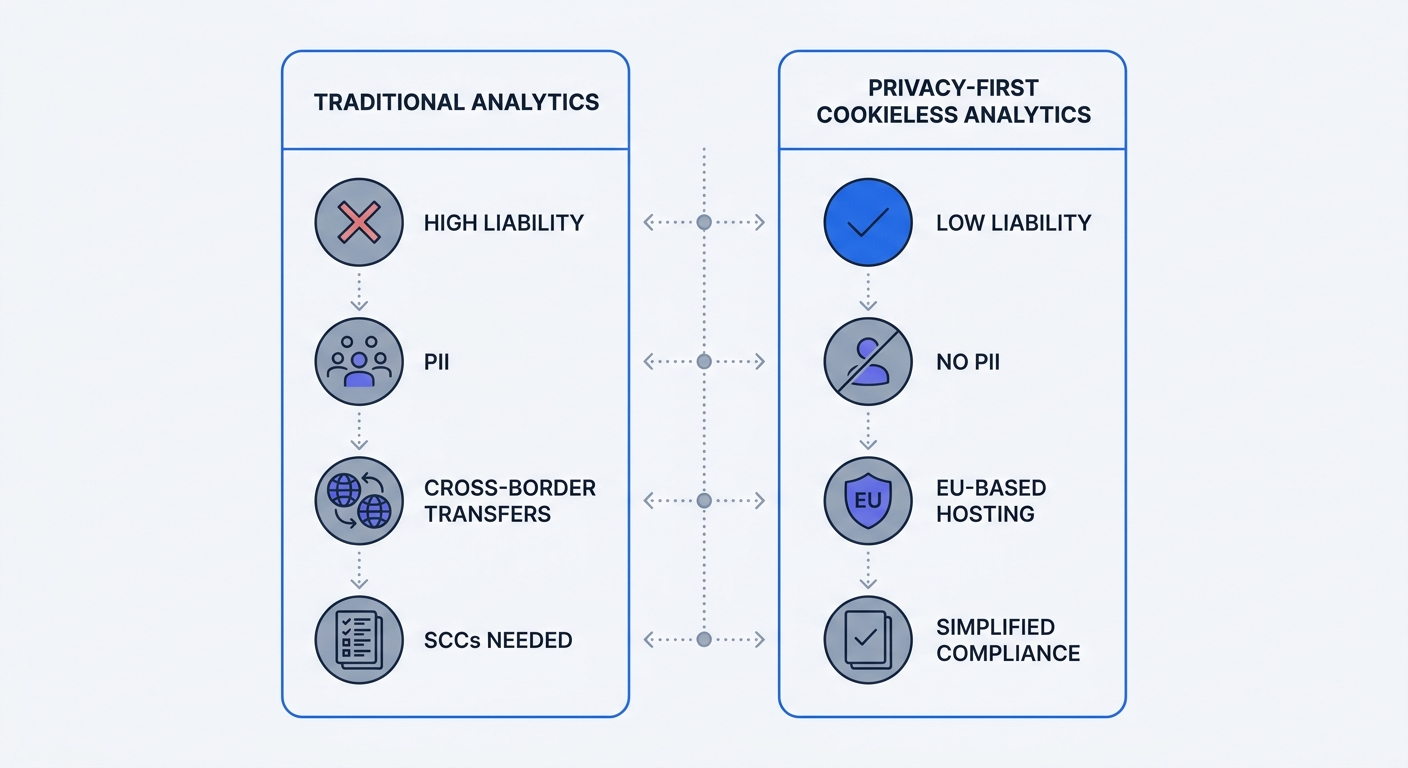
Web analytics tools create immense compliance friction. Legacy platforms like Google Analytics operate as massive data processors. They collect IP addresses, device identifiers, and cross-site tracking cookies.
Standard analytics setups capture granular user identifiers. The script records the visitor's IP address before dropping an alphanumeric cookie into the browser cache. The software pings a US-based server with this payload on every page load.
Regulators classify IP addresses and tracking cookies as personal data. Austrian and French data protection authorities ruled standard Google Analytics configurations non-compliant. They determined the data transfer mechanism failed to prevent US intelligence agencies from accessing European user data.
Using legacy platforms requires a massive compliance infrastructure. Engineers must deploy consent management platforms. Legal teams must draft complex Transfer Impact Assessments. Marketing teams lose data visibility when users click "Reject All" on the cookie banner.
Review your website source code. Identify legacy tracking scripts. Calculate the hours your legal team spends managing consent frameworks and transfer agreements for these legacy tools.
The Swetrix Privacy-First Advantage
Eliminating personal data collection simplifies legal requirements. Privacy-by-design architecture changes the vendor relationship. When you stop collecting identifying information, the compliance burden vanishes.
Swetrix operates as a cookieless, open-source analytics platform. The system avoids cookies. Tracking users across devices remains impossible. The codebase strips identifiable information from the traffic data before storage.
Cookieless analytics shifts the legal baseline. Swetrix hashes user data at the edge. The system drops the raw IP address before the payload reaches the database. We generate an anonymous, rotating session identifier that expires at the end of the day.
Providing analytics services constitutes data processing, even without identifying markers. Swetrix offers a streamlined Data Processing Agreement to formalize this relationship. This document serves as an operational guarantee rather than a high-risk liability shield. The contract confirms your ownership of the aggregate data, guaranteeing the infrastructure resides on European servers.
This minimal data footprint creates broad compliance. Stripping identifiers removes the need for cookie consent banners. It satisfies the strict requirements of cookies and the law. Bypassing health data collection means healthcare clients avoid signing a Business Associate Agreement for HIPAA compliance.
Open your analytics dashboard. Export your historical reports. Switch to a privacy-by-design platform to end your reliance on complex tracking agreements and foreign data transfers.
Stop managing complex consent frameworks for basic website metrics. Swetrix delivers accurate, compliant traffic data without the legal liability of legacy trackers. Start your free Swetrix trial today and simplify your privacy stack.